When I started in IT many moons ago, the concept of DevOps was not even a glimmer in the eye of Patrick Debois, My then manager, explained security in information technology with an analogy; that analogy was one of a house; at the time, it was based on layered security, and it went something like this. A house is a system of computing units and services; different rooms have different purposes. To enter your house, you need a key; the front door keys should differ from your back or Garage door keys.

Once in your house, you have your rooms, a bathroom, a kitchen, the lounge, the dining room, a few bedrooms, and a bathroom; you may have a basement or attic (loft). Each room has a different purpose and may have a lock on the door to gain entry, for example, the bathroom.
Each of these rooms equates to your security zones, a DMZ, where you have full access, could be analogous to your lounge; within each room, there are areas, for example, drawers or cupboards, that have general access requirements and others that have a requirement to be locked for added protection. These are your applications and datasets. For example, your child may have access to the TV remote but needs a code to purchase a film. You may have a lock on the medicine cabinet; these are an analogy for Role Based Access controls (RBAC).
At the time, it was quite a sophisticated analogy for a simpler time; dial-up internet and remote access was serial-based and painfully slow. Why am I telling a story of an age gone by? We know that things are so different today and much more complicated, but I feel that the analogy has stood the test of time so well that I still use it; and like most houses owned for a long time, I’ve extended it; I now have a front garden with a gate, a porch and a honeytrap in the garden shed – don’t ask 😊.
A couple of IT buzzwords in the security space are “The Edge” and “SASE”. The Edge is the network perimeter where various devices, such as sensors, cameras, smartphones, and IoT equipment, generate, process, and consume data. Edge computing enables faster response times, lower bandwidth costs, and better user experience by bringing computation closer to the data source. However, it also introduces more complexity, diversity, and risk to the DevOps and DevSecOps processes. It also dramatically increases the risk to a business because instead of reducing service attack points, it will increase potential attack points at your most vulnerable and challenging-to-protect layer.
SASE is an acronym for Secure Access Service Edge. It relates to a network architecture that combines SD-WAN (Software-Defined Wide Area Network) and cloud-native security services to deliver secure and optimized connectivity to any device or application at the Edge.
You may be asking where we are going? Well recently I read this on linkedin:
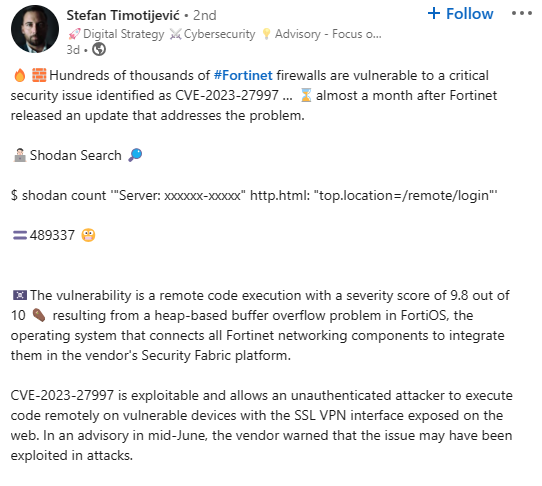
In the comments, the author linked to an excellent article on Bishop Fox, where they stated that a month after Fortinet fixed the vulnerability contained in [CVE-2023-27997, 69% of FortiGate Firewalls Are still Vulnerable] to attack. This is a seriously worrying number as a firewall is the primary line of defence in any perimeter. But this vulnerability is not even the tip on the tip of the top of the iceberg; as the Edge grows, more and more devices will need to be monitored and updated.
So how can DevOps help?
Well, remember the little brother with a big attitude DevSecOps. DevSecOps extends the DevOps approach by integrating security into every stage of the project lifecycle, from code to cloud. DevOps and DevSecOps will face new challenges and opportunities as more applications and services move to the Edge. SASE products can help DevOps and DevSecOps teams simplify network management, enforce consistent security policies, optimize performance, and reduce costs across the edge environment.
Some of the challenges for DevOps and DevSecOps at the Edge are:
- Scaling: Edge applications may need to run on thousands or millions of devices across different locations, networks, and platforms. This requires a scalable, flexible infrastructure that supports dynamic provisioning, configuration, monitoring, and updating edge devices and applications.
- Diversity: Edge devices vary in hardware capabilities, operating systems, protocols, and standards. This requires a heterogeneous and interoperable environment supporting different types of devices and applications with minimal friction and overhead.
- Security: Edge devices are exposed to more threats than cloud or on-premises servers, as they may be physically accessible, tampered with, or compromised by malicious actors. This requires a robust and comprehensive security strategy that can protect the Edge’s data, devices, and applications from unauthorized access, manipulation, or leakage.
To address these challenges, DevOps and DevSecOps teams must adopt new tools and practices that enable automation and visibility across the edge environment. Some of the possible solutions are:
- Hashicorp Boundary: This secure access management solution allows DevOps and DevSecOps teams to access any system at any location without exposing network details or requiring VPNs. Boundary uses identity-based authentication and authorization to grant granular access to edge devices and applications based on policies and roles. Boundary also provides audit logs and telemetry data for monitoring and compliance purposes.
- Vulnerability scanning and management: This identifies and resolves security weaknesses in edge devices and applications. Vulnerability scanning and management tools can help DevOps and DevSecOps teams to continuously monitor and manage edge security posture by detecting vulnerabilities, prioritizing risks, applying patches, and verifying remediation. Tooling like Nessus Professional or Qualys Vulnerability Management, when configured correctly, can detect vulnerabilities in OS’es, Applications and Network Devices, they can even integrate into existing pipelines to create a complete workflow potential exposure to slamming the door shut.
Summary
The Edge is an evolving landscape, Edge devices like Sensors, IP Enabled cameras, are adding to complexity and monitoring requirements. Current edge devices, line VPN,s and Firewalls are proving vulnerable to many issues and are not being fixed. This is an oporunity for DevOps and DevSecOps teams to take the lead and achieve automation and visibility in a distributed edge environment by leveraging new solutions to protect the edge. Doing so will help them deliver faster, more reliable, and more secure edge applications and services that meet the evolving needs of users and businesses.



